After days of waiting, refreshing my inbox, and checking the result again and again, it finally happened.
I’m proud to share that I successfully passed the HTB Certified Active Directory Pentesting Expert (CAPE) certification by Hack The Box with a perfect score: 10 out of 10 flags.

For me, CAPE was not just another certification. It was a serious test of my Active Directory penetration testing skills, my methodology, my patience, and my ability to explain technical attack paths in a professional report.
This blog is my personal review of the exam, including how I prepared, how I planned my budget, what skills I focused on, and what I learned from the experience.
What is CAPE?
HTB Certified Active Directory Pentesting Expert (CAPE) is an advanced certification from Hack The Box that focuses on real-world Active Directory penetration testing.

The exam is designed to test whether a candidate can compromise complex Active Directory environments by identifying misconfigurations, chaining attack paths, escalating privileges, moving laterally, and documenting the full compromise process clearly.
In my opinion, CAPE is not only about knowing tools. It is about understanding how Active Directory works, how different weaknesses connect together, and how to turn small pieces of information into a complete attack path.
Why I Took CAPE
I decided to take CAPE because I have always been looking for deeper Active Directory challenges across different certifications and training paths.
Throughout my offensive security journey, I have explored and challenged myself with several certifications and courses related to penetration testing, red teaming, and Active Directory security, including OSCP, OSEP, CRTO, C-ADPenX, and other certifications in my portfolio. Each of them helped me grow in different areas, but I wanted to continue pushing myself further in the Active Directory space.

Active Directory has always been one of the most important areas in internal penetration testing and red team operations. In many real-world environments, AD is the core of identity, access control, authentication, and business operations. If an attacker compromises Active Directory, the impact can be severe and may lead to full domain compromise.
For me, CAPE was not just another certification to add to my profile. It was a challenge I had already set for myself. I made a clear commitment that I would take it, push through the preparation, and pass it.
I wanted to test my ability in AD exploitation, post-exploitation, lateral movement, attack path analysis, and professional reporting under exam conditions.
CAPE represents another important milestone in my offensive security journey, and passing it proved to me that persistence, preparation, and discipline can turn a difficult goal into an achievement.
How CAPE Compares to Other Certifications
One question I often get is how CAPE stacks up against other certs I’ve taken. Here’s a brief comparison:

CAPE is the deepest pure-AD exam I’ve taken. Unlike OSEP or CRTO, there’s no evasion component the focus is entirely on understanding and exploiting AD relationships, permissions, and trust configurations.
You can also read my previous certification journeys:
How I Prepared
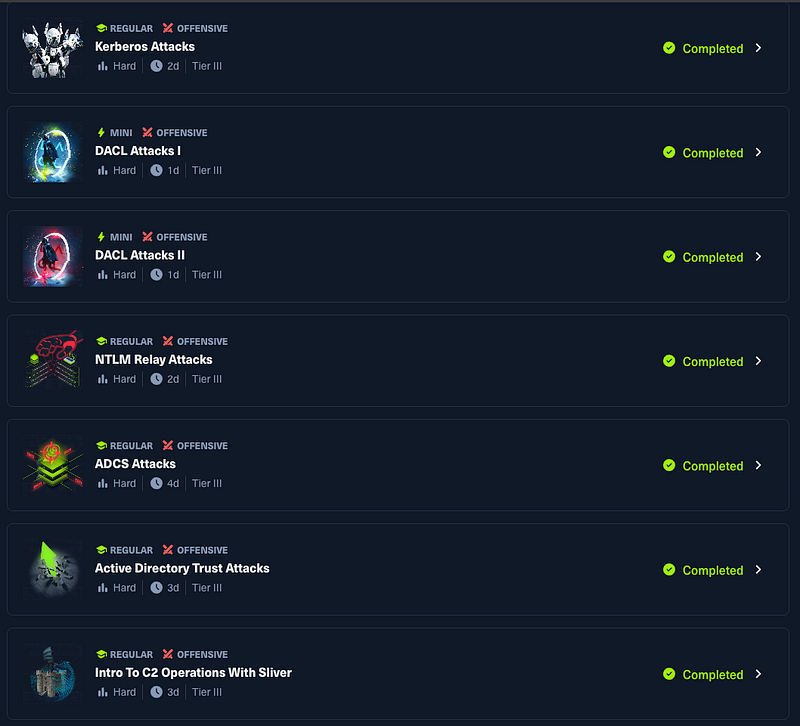
To be eligible for the CAPE exam, candidates must first complete the CAPE Certification Path(https://academy.hackthebox.com/app/paths/417) on HTB Academy, which falls under the (https://academy.hackthebox.com/app/paths/417) Job Role Path.
This path consists of 15 modules that cover the core skills required for the exam. You cannot attempt the exam without completing this path first.

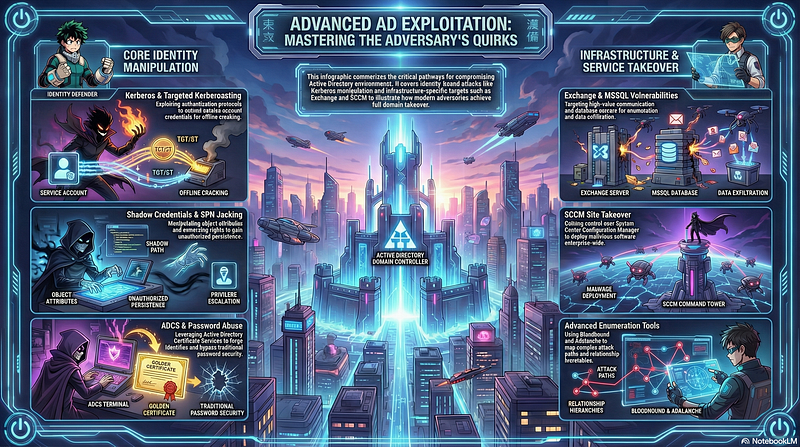
The Knowledge
1. AD Fundamentals
No shortcuts here. I reviewed domain structure, Kerberos and NTLM authentication, Group Policy, trusts, delegation, Certificate Services, and access control. Without a solid foundation, everything else falls apart.
2. Enumeration Methodology
Enumeration isn’t just the first step; it’s the step you keep coming back to. I practiced collecting domain users, groups, local admins, SMB shares, LDAP data, ACLs, SPNs, delegation settings, trust relationships, certificate templates, and network routes.
The real skill isn’t running the tools it’s reading the output, filtering noise, and deciding what to investigate next.
During preparing for CAPE, I also created my own helper tool called BigBlack-NXC, built around NetExec (NXC), to support my enumeration workflow. It covers SMB/LDAP enumeration, user and group discovery, share discovery, credential validation, and basic attack surface mapping. But the most important lesson from building it was this:
Tools can help you enumerate faster.
But methodology helps you understand what matters.
3. Attack Path Analysis
In AD, one credential rarely gives you the domain controller directly. Instead, that credential leads to a host, which exposes another credential, which has access to another system until the full path emerges.
BloodHound was essential for visualizing relationships (users, groups, sessions, ACLs, local admin rights, delegation paths). But I never used it as an answer machine. I used it as an analysis tool and always validated findings manually. Questions I kept asking myself:
- What can I access with this account?
- Can this permission actually be abused in this environment?
- Can this host lead me to another segment?
- Is this BloodHound path exploitable, or is it theoretical?
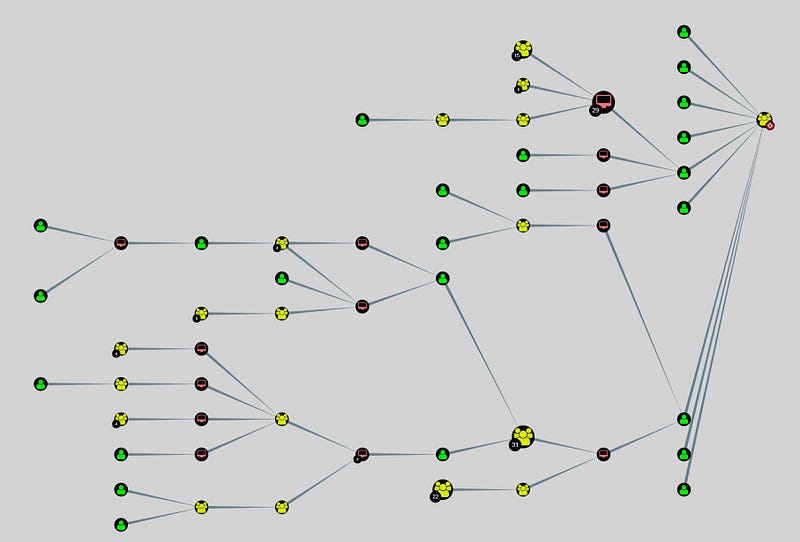
BloodHound can show you the graph, but you still need to understand the story behind the graph.
4. Kerberos and Delegation Abuse
Kerberoasting, AS-REP Roasting, S4U2Self/S4U2Proxy, Constrained and Resource-Based Constrained Delegation, cross-trust scenarios I reviewed all of them. The key wasn’t memorizing command syntax; it was understanding the ticket flow logic. If you understand the concept, troubleshooting becomes straightforward.

5. ACL and Permission Abuse
GenericAll, GenericWrite, WriteDACL, WriteOwner, ForceChangePassword, AddMember, AllowedToDelegate, WriteSPN these permissions look small in isolation but become extremely powerful in the right context. I practiced ACL abuse until it felt natural. This is one of the most practical skills for both CAPE and real-world internal pentesting.
6. Reporting Practice
CAPE scores your report. I prepared a template covering Executive Summary, Scope, Attack Path Summary, Technical Findings with Evidence, Business Impact, Remediation Advice, and Conclusion. A good report doesn’t just prove compromise it explains how it happened, why it matters, and how to fix it.
Budget Summary
Preparing for the HTB Certified Active Directory Pentesting Expert (CAPE) required both time and financial planning. Since CAPE is connected to HTB Academy modules, the total cost was not only the exam voucher itself, but also the cubes and subscription used to complete the required modules.

Note: After completing the 15 modules, I received 1,420 cubes back, which helped offset future HTB Academy content.
Some parts of this journey were supported by my family, and I’m grateful for that. Certifications require not only effort and discipline but also resources to access the right materials.
For me, this was a meaningful investment not just for the certificate, but for the structured methodology, sharpened enumeration mindset, and reporting discipline I gained.
My Exam Experience
The exam was challenging and required a lot of focus.
For me, CAPE was genuinely difficult. It was not the kind of exam where I could simply follow a checklist and expect everything to work smoothly. The environment felt realistic because the attack path was not always obvious. Some information looked useful at first but turned out to be noise, while some small details that looked minor later became important.
The hardest part was not only exploiting vulnerabilities.
The hardest part was deciding where to go next.
During the exam, I had to constantly review my notes, re-check enumeration results, validate assumptions, and connect different pieces of information together. There were many moments where I felt stuck, stepped back, and asked myself what I had missed.
Honestly, during the exam, I lost count of how many times I said:
“This is hard.”

But that’s exactly what made it meaningful. CAPE forced me to stay calm, slow down, and trust my methodology instead of throwing random attempts at the wall. The cycle was always the same:
Enumerate → Validate → Exploit → Document → Repeat.
One specific lesson: when I got stuck at a pivotal point midway through the exam, I almost went down a rabbit hole chasing a complex attack that looked right. Instead, I forced myself to go back to enumeration basics, and within an hour I found a small detail I’d overlooked — a permission that opened up the next segment entirely. That moment reinforced something I already believed but now felt: thoroughness beats cleverness.
One thing I want to highlight: Flag 1 is the turning point.
It's the moment that tells you whether you'll push forward or stop here. If you struggle too long on Flag 1, it can drain your time and confidence for everything that comes after. But if you approach it with solid enumeration and a clear methodology, it becomes the foundation that carries you through the rest of the exam. For me, Flag 1 was where I proved to myself that my preparation was enough and that the rest was about staying disciplined, not panicking, and trusting the process.
When I finally completed the attack path and submitted the report, I knew this exam had truly tested my patience, discipline, and AD methodology.
Then came the wait. Almost 20 days

of checking my email, refreshing my inbox, hoping every notification was the result. When the message finally arrived passed that moment made every difficult hour worth it.

Next I Claimed My Certificate

That moment made all the effort worth it.
CAPE was not only a certification exam for me. It was a challenge that tested my Active Directory methodology, my discipline, my patience, and my ability to keep going even when things were difficult.
Thank you to Hack The Box for creating a challenging and realistic certification experience.
Pro Tips for Future CAPE Candidates
If you are planning to take CAPE, here is my advice:
- Complete the CAPE path properly. Don’t rush the modules just to unlock the exam — the knowledge compounds.
- Build your own AD enumeration checklist. Generic checklists won’t cover everything; tailor one to your workflow.
- Validate BloodHound findings manually. Not every path on the graph is exploitable.
- Understand Kerberos and delegation deeply. Know the why, not just the how.
- Practice ACL abuse until it’s muscle memory.
- Take screenshots and notes from the very first minute. Your report depends on it.
- Prepare your report template before the exam. You don’t want to be formatting headers under time pressure.
- When you’re stuck, go back to enumeration. The answer is almost always something you haven’t enumerated yet.
- Stay calm and trust your methodology. Panic leads to rabbit holes.

What’s Next
After passing CAPE, the first thing I should do is rest.
The preparation and exam demanded intense focus over a long period late nights, constant practice, and mental pressure that doesn’t stop even after you submit the report. I’ve learned that pushing hard is important, but so is knowing when to step back and recharge. Burnout doesn’t help anyone grow.
Once I’ve recharged, the plan is clear. I want to take the skills I sharpened through CAPE structured enumeration, attack path analysis, permission abuse, and professional reporting and apply them more deeply in real-world red team engagements and AD security assessments. CAPE validated my methodology, but it also showed me areas where I want to go even further.
The goal hasn’t changed: keep learning, keep improving, keep pushing forward.
— — — —Thank you for reading— — — —
Good luck, and feel free to reach out if you need tips on specific sections!
My Contact: https://sabastiaz.github.io/contact.html
My Tools: https://github.com/sabastiaz/BigBlack-NXC