Hi everyone! My name is Ratthapong Sommanus, but you can call me “Black”.
I’m also known as “Sabastiaz”.
Today, I will be reviewing the Certified Red Team Analyst (CRTA) certification in Cyber WarFare
Before Exam
I had never heard of this certification provider before until a friend (Chicken0248) introduced it to me last year. However, at that time, I wasn’t particularly interested. As expected, my friend (Chicken0248) brought it up again, saying, “The certification looks really cool, and it’s on sale right now!” With the added temptation of a discount — just enter the code “JOASx90” to get 90% OFF — I didn’t hesitate and bought it immediately.
So, after purchasing the exam voucher I have email purchase success and I have 2 accounts for access lab and portal live I access to portal lab and I take lab right now I have long time to take lab maybe 5 hour I complete this lab
So, after I passed the lab, I sent an email to support to reserve my exam schedule for the next day.
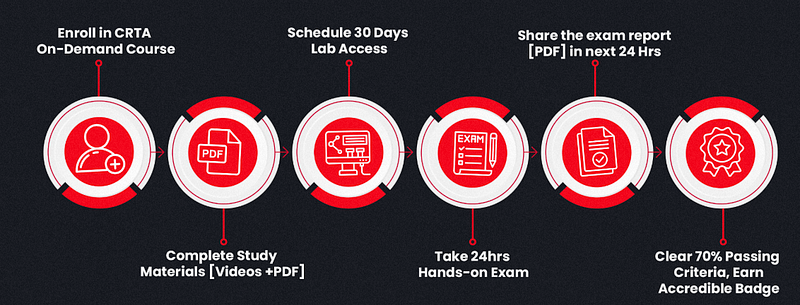
Certification Procedure
Couse Syllabus
The courses contents are divided across 5 sections listed below:
- Introduction to Red Teaming
- What is Red Teaming?
- Red Team Attack Lifecycle (Phases)
- Red Team Infrastructure (Nomenclature)
- Enterprise Environment Overview
- Technologies Exploitation in Red Teaming (Web, Network, Cloud)
2. Red Team Lab setup
- Virtual Environment Setup & Configuration
- Setting up Attacker Machine
- External Red Team Lab Setup
- Network Pivoting Setup
- Internal Red Team Lab Setup (Active Directory Setup)
3. External Offensive Operations
- External Infrastructure Overview
- Enumerating & Mapping External exposed assets
- Externally exposed service exploitation
- Exploitation (Web & Network based)
- Post-Exploitation (Web & Network based)
4. Internal Offensive Operations
- Internal Infrastructure Overview
- Enumerating & Mapping Internal assets
- Infrastructure Enumeration (Active Directory Environment)
- Bypassing Network Segmentation (Firewalls)
- Active Directory Phases Exploitation (Initial Recon to Domain Admin)
5. Practical Case Study (Hands-on Lab)
- Accessing the Lab
- Lab Architecture
- Mapping the Lab with MITRE ATT&CK Framework
- External Red Teaming
- Internal Red Teaming
- Utilizing LOLBAS for stealth persistence & Data Exfiltration
- Preparing for Examination
Do you think the exam is easy?
That’s not true — it’s actually really hard!
Exam
30 Minutes Before the Exam:
You will receive the necessary exam details, including VPN credentials (Username & Password) and the Scope of Engagement.
One thing I really liked was that the exam presents a realistic objective, making it feel like an actual engagement
The exam feels like a real penetration test, but in my opinion, it’s more like an Active Directory (AD) pentest because most of the exploitation steps involve AD. There are also many rabbit holes, making it even more challenging.
That being said, this exam is beginner-friendly for those looking to earn their first red team certification, as it provides a structured approach to learning AD exploitation and real-world attack scenarios.
The most important thing isn’t how many systems you can exploit, but rather not forgetting to submit your report within 24 hours after the exam ends.
Final Thoughts
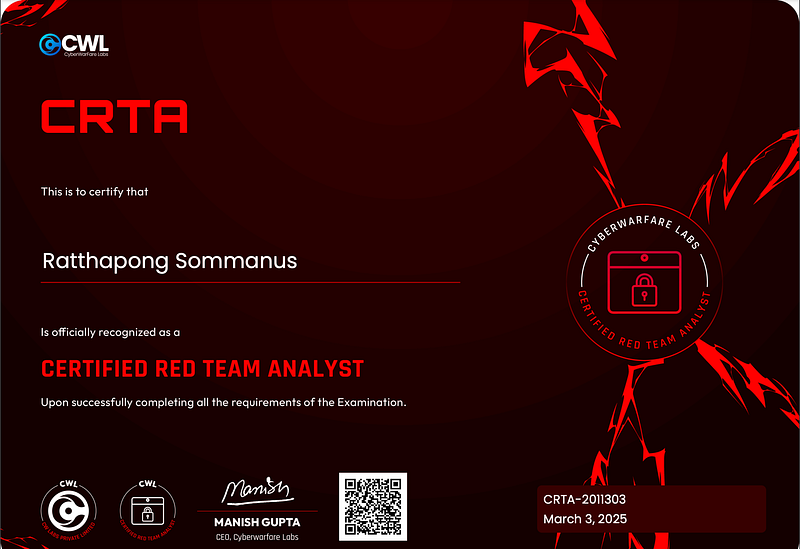
The CRTA exam was a challenging yet rewarding experience, pushing me to think critically and apply real-world Active Directory pentesting techniques. If you’re looking for a hands-on certification that simulates an actual red team engagement, this is definitely worth pursuing!
I received my exam results in just one day — I passed! I was so excited because this certification is really cool.
The certification is really cool!
You can connect with me on my social accounts:
[HackTheBox] : https://app.hackthebox.com/users/190672
[linkedin] : https://www.linkedin.com/in/ratthapong-sommanus-465b661b2/
[Facebook] : Ratthapong Sommanus
If you’re interested, you can check it out here: Cyber Warfare